### 011 Mastering
./ Broken Access Control (BAC)
What is Broken access control? | // Detection! // Exploitation! // Prevention!
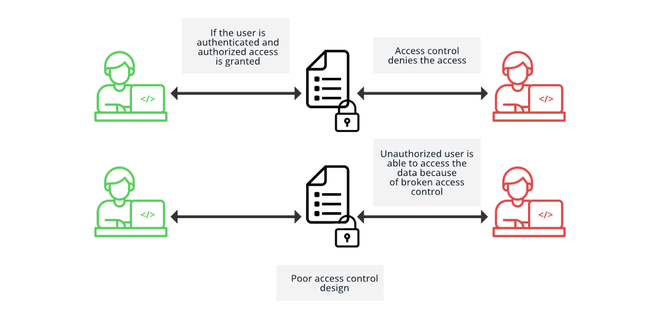
Access control (or authorization) is the application of restrictions on who can perform attempted actions or access the resources that they have requested.
It is a critical vulnerability which was moved from 5th position in 2017 to 1st position in 2021 as per OWASP Top 10 awareness document. Access control enforces policy such that users cannot act outside of their intended permissions. Failures typically lead to unauthorized information disclosure, modification, or destruction of all data or performing a business function outside the user’s limits.
Mainly access control is dependent on authentication and session management:
- Authentication identifies the user and confirms that they are who they say they are.
- Session management identifies which subsequent HTTP requests are being made by that same user.
- Access control determines whether the user is allowed to carry out the action that they are attempting to perform.
Again there are 3 varities of access controls:
- Vertical access controls
- Horizontal access controls
- Context-dependent access controls
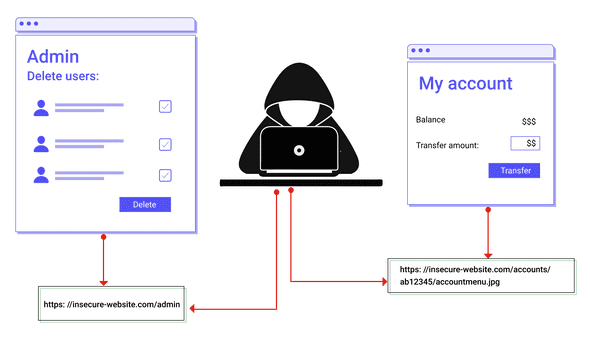
Vertical access controls are mechanisms that restrict access to sensitive functionality that is not available to other types of users. With vertical access controls, different types of users have access to different application functions. For example, an administrator might be able to modify or delete any user’s account, while an ordinary user has no access to these actions. Vertical access controls can be more fine-grained implementations of security models designed to enforce business policies such as separation of duties and least privilege.
Horizontal access controls are mechanisms that restrict access to resources to the user groups who are specifically allowed to access those resources.
With horizontal access controls, different users have access to a subset of resources of the same type. For example, a banking application will allow a user to view transactions and make payments from their own accounts, but not the accounts of any other user.
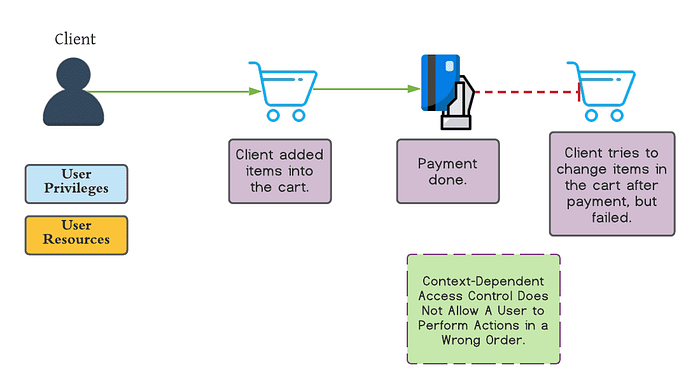
Context-dependent access controls restrict access to functionality and resources based upon the state of the application or the user’s interaction with it. Context-dependent access controls prevent a user performing actions in the wrong order. For example, a retail website might prevent users from modifying the contents of their shopping cart after they have made payment.
That’s for now let’s cover after a coffee…
